Adding Entra ID credentials to Azure Key Vault
I asked Microsoft Copilot to help me move some Azure Entra ID configuration from appsettings.json to Azure Key Vault. My exact question was:
In appsettings.json I have the following (with some values removed)
"AzureAd": {
"Instance": "https://WebCashFlow.ciamlogin.com/",
"Domain": "WebCashFlow.onmicrosoft.com",
"TenantId": "tenantID",
"ClientId": "clientID",
"ClientSecret": "clientSecret",
"CallbackPath": "/signin-oidc",
"SignedOutCallbackPath": "/signout-callback-oidc",
"SignedOutRedirectUri": "/",
"RemoteSignOutPath": "/signout-oidc" // optional but good to include
},
Firstly, which of the above can I safely keep in appsettings.json?
Secondly, can you give me a step by step guide to moving the other items to Azure Key Vault. (I use Visual Studio Insiders, if any part can be done from within VS.)?
This is answer I received. and the process I followed.
Part 1 – What can safely stay in appsettings.json?
Here is your configuration again, classified line by line:
"AzureAd": {
"Instance": "https://WebCashFlow.ciamlogin.com/",
"Domain": "WebCashFlow.onmicrosoft.com",
"TenantId": "tenantID",
"ClientId": "clientID",
"ClientSecret": "clientSecret",
"CallbackPath": "/signin-oidc",
"SignedOutCallbackPath": "/signout-callback-oidc",
"SignedOutRedirectUri": "/",
"RemoteSignOutPath": "/signout-oidc"
}
SAFE to keep in appsettings.json:
These are identifiers or URLs, not secrets:
- Instance
- Domain
- TenantId
- ClientId
- CallbackPath
- SignedOutCallbackPath
- SignedOutRedirectUri
- RemoteSignOutPath
These values are routinely visible in front end requests and metadata endpoints. Keep them exactly where they are.
MUST be moved to Azure Key Vault
Why?
- It is a credential
- Anyone who gets this can impersonate your app against Entra ID
- Treat it with the same care as a database password or Stripe secret key
Part 2 - Target end state
At the end of this step:
| Location |
Contains |
| appsettings.json |
Non‑sensitive AzureAd settings |
| Azure Key Vault |
AzureAd--ClientSecret |
| Code |
No changes to authentication code |
Your app will still read Configuration["AzureAd:ClientSecret"], but Key Vault will supply it instead of a file.
Part 3 - Step by step: Move ClientSecret to Azure Key Vault
Step 1 – Create an Azure Key Vault
Azure Portal (recommended for first time)
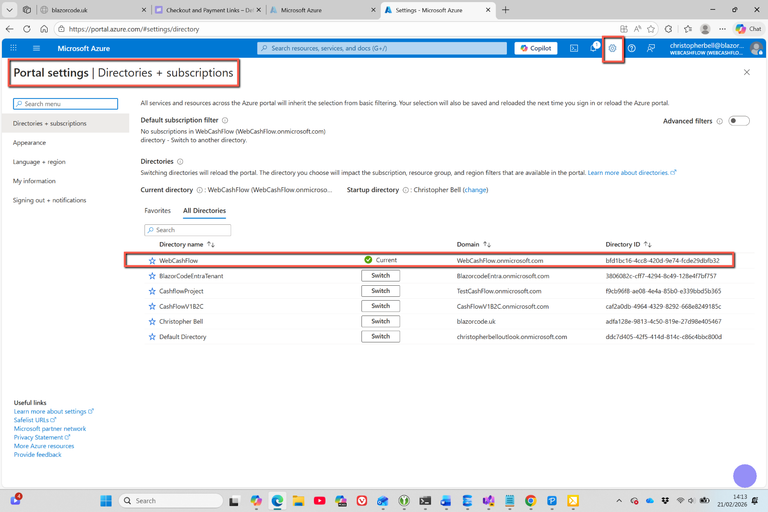
Before getting into the detail, I have a question. Having logged into the Azure portal, the first question is 'Which Directory'. These are the directories I appear to have:
| Directory Name |
Domain |
DirectoryID |
| Christopher Bell |
blazorcode.uk |
adfa128e-9813-4c50-819e-27d98e405467 |
| BlazorCodeEntraTenant |
BlazorcodeEntra.onmicrosoft.com |
3806082c-cff7-4294-8c49-128e4f7bf757 |
| CashflowProject |
TestCashFlow.onmicrosoft.com |
f9cb96f8-ae08-4e4a-85b0-e339bbd5b365 |
| CashFlowV1B2C |
CashFlowV1B2C.onmicrosoft.com |
caf2a0db-4964-4329-8292-668e8249185c |
| Default Directory |
christopherbelloutlook.onmicrosoft.com |
ddc7d405-42f5-414d-814c-c86c4bbc800d |
| WebCashFlow |
WebCashFlow.onmicrosoft.com |
bfd1bc16-4cc8-420d-9e74-fcde29dbfb32 |
It is not clear to me which directory I should use. The ones I can (probably) discount are:
| Directory Name |
Reason |
| Christopher Bell |
Possible? Default directory |
| BlazorCodeEntraTenant |
Possible? Entra ID directory for WebCashFlow |
| CashflowProject |
Probably not. Original for Charles Sanderson? |
| CashFlowV1B2C |
Probably not. Looks like Azure B2C for original CashFlow |
| Default Directory |
Definitely not. Old personal account directory |
| WebCashFlow |
Possible? |
- By switching to 'WebCashFlow' I can see that this directory contains the Entra ID users for my WebCashFlow project, so this could be possible. However, when I tried to 'create a resource' in this directory I got a message that stated there was no Azure subscription for this directory - so could not create any resource.
- I faced the same problem after switching to 'BlazorCodeEntraTenant'. This looks to be another directory used for Entra ID testing, but had fewer users than WebCashFlow, so probably isn't the 'live' Entra ID directory for WebCashFlow users.
- Switching directory to 'CashFlowProject' required 2FA which I was unable to provide, so not that directory.
- Switching directory to 'CashFlowV1B2C' also required 2FA which I was unable to provide, so not that directory.
- It definitely isn't going to be the directory associated with my personal Outlook account, so by a matter of elimination, it must be the directory associated with 'blazorcode.uk'
I therefore assume I should use the 'blazorcode.uk' directory.
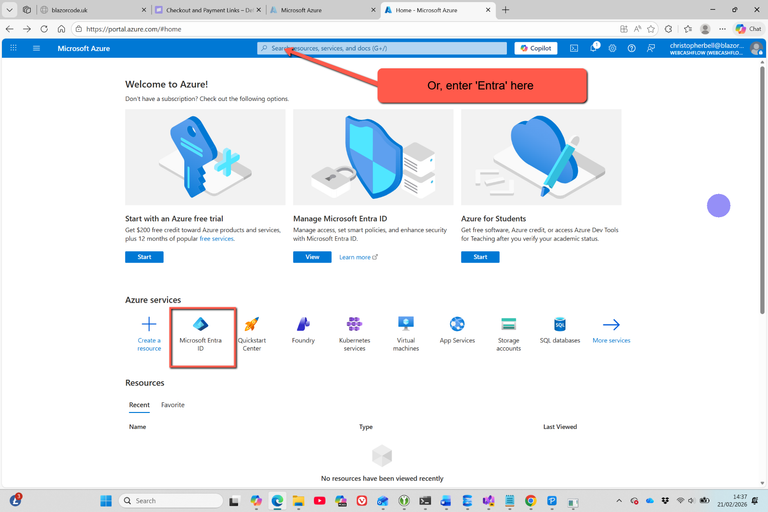
- Go to Azure Portal → Create a resource
- Search for Key Vault
- Create
- Select Subscription
- Select Resource Group (or add a new resource group)
- Name: wcf-keyvault (This is the name I ended up with, the screenshot shows my first attempt, with a different name.)
- Region: UK South
- Pricing tier: Standard
- Leave networking as default for now
- Create the vault
Step 2 – Add the Client Secret to Key Vault
I got as far as creating the Azure Key Vault, however when I tried to add a Secret I got the following error message “The operation is not allowed by RBAC. If role assignments were recently changed, please wait several minutes for role assignments to become effective. “
The answer to this problem was to give myself permission to add secrets.
- In the Key Vault:
- Select Access Control (IAM)
- Select + Add
- In the Roles tab
- Enter Key Vault Secrets Officer in the Search box
- A list should be displayed; highlight Key Vaults Secrets Officer and click Next
- On the Members tab
- Select + Select Members
- In the right-hand pane, highlight the member and click Select
- The right-hand pane will close and the member will be displayed in the main pane. Select Review + assign
Add the Client Secret to Key Vault
- In the Key Vault:
- Select Objects
- Select Secrets
- Click + Generate/Import
- Set
- Name: AzureAd--ClientSecret
- Value: your actual Entra ID client secret
- Create
Note the double dashes (--). This maps automatically to AzureAd:ClientSecret.
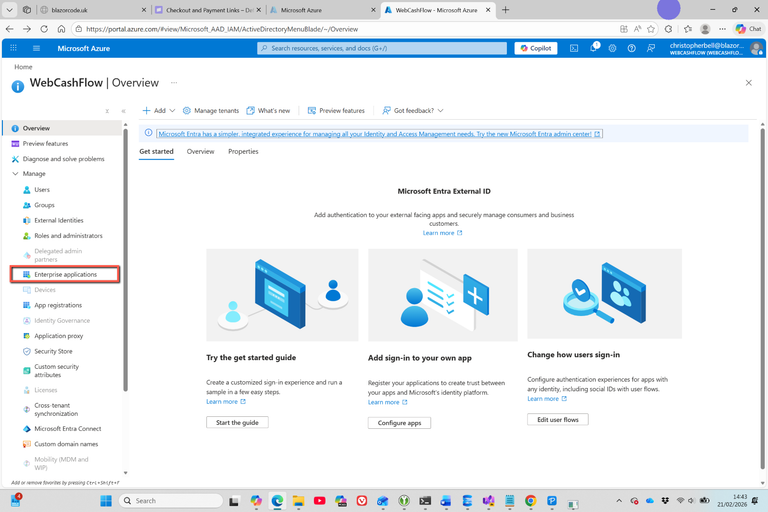
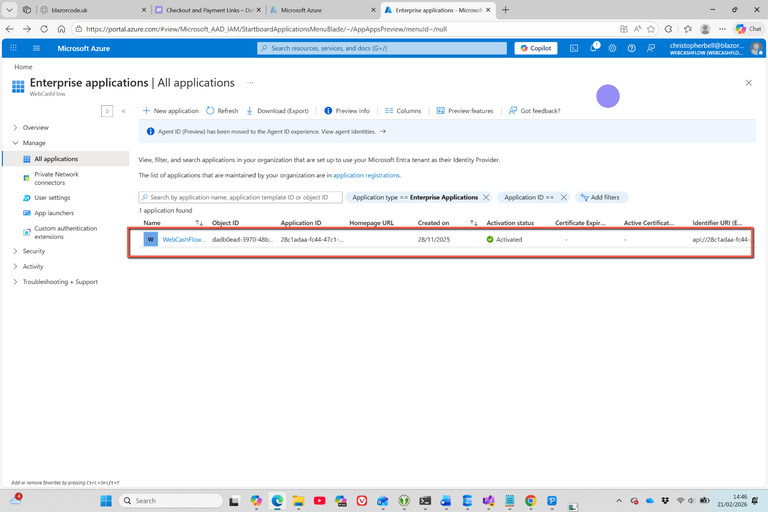
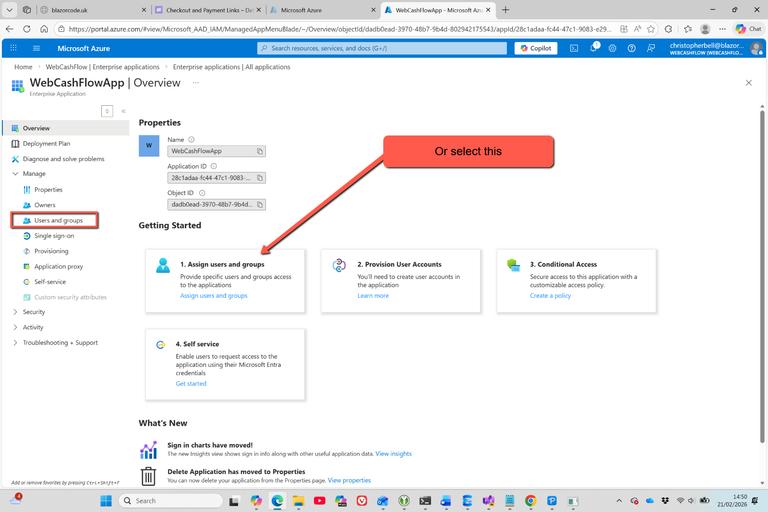
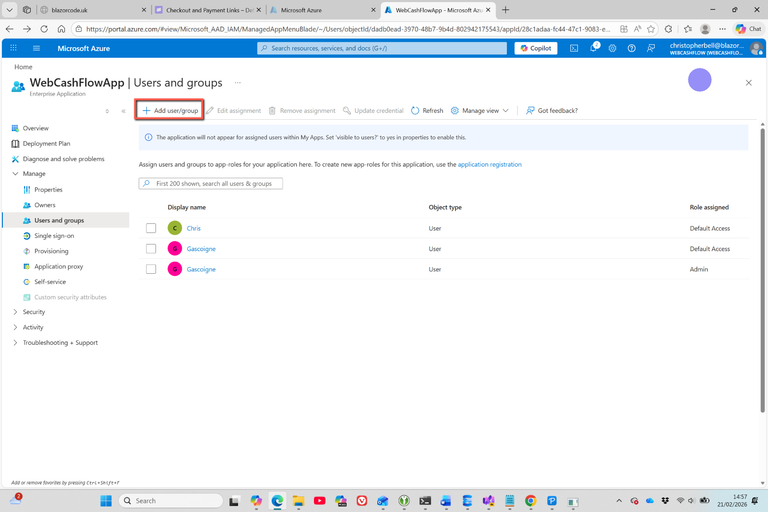
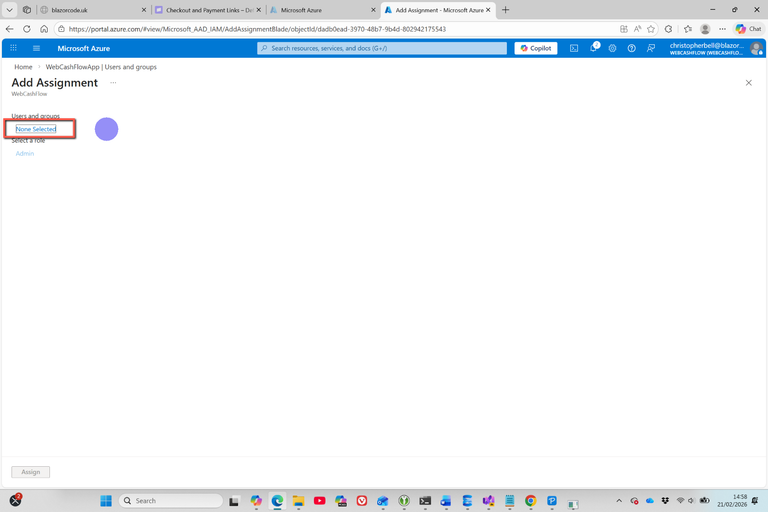
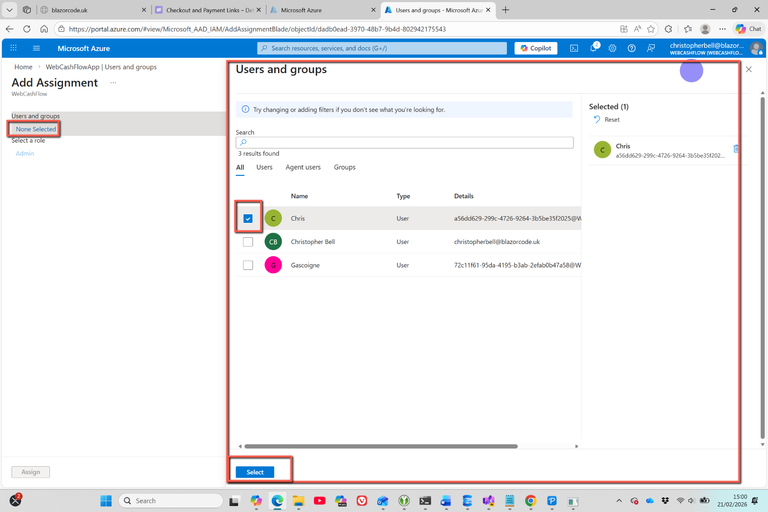
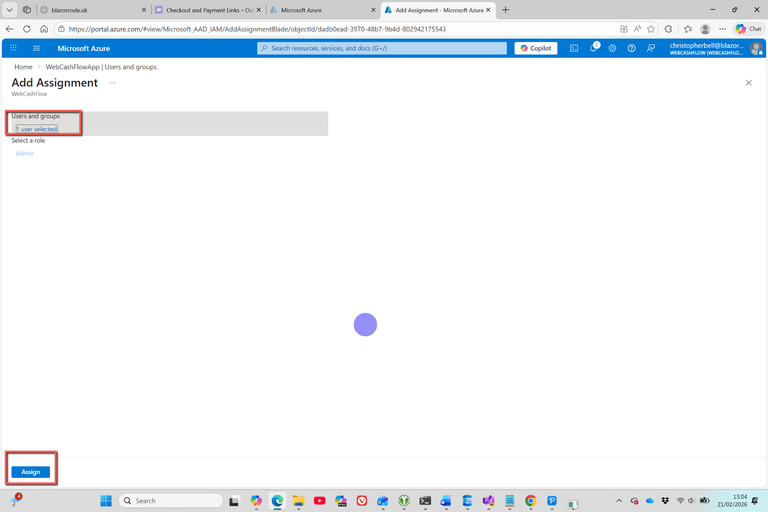
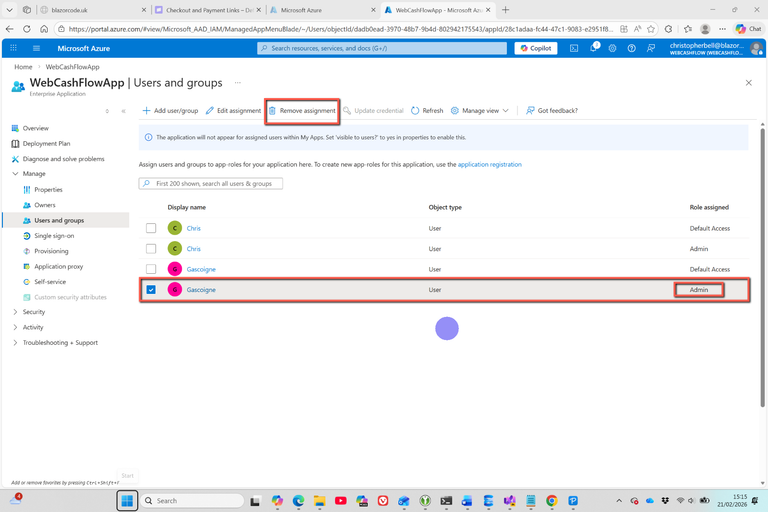
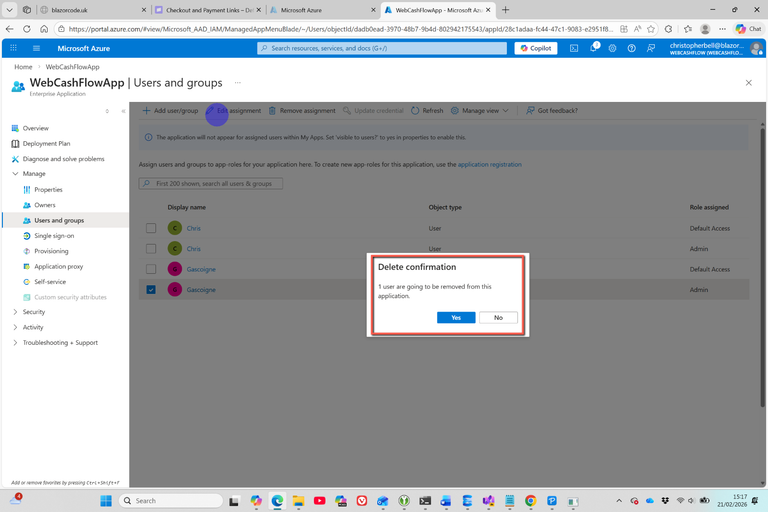
Step 3 – Allow your app (developer) to read the secret
For now we’ll use your own Azure identity so you can test locally.
- In Key Vault → Access control (IAM)
- Add role assignment:
- Role: Key Vault Secrets User
- Assign access to: User
- Member: your Azure login
Step 4 – Install required NuGet packages
In Visual Studio, add NuGet packages:
- Azure.Identity
- Azure.Extensions.AspNetCore.Configuration.Secrets
Step 5 – Wire Key Vault into Program.cs
Open Program.cs
At the top of the file insert:
using Azure.Identity;
using Azure.Extensions.AspNetCore.Configuration.Secrets;
Add, after var builder = WebApplication.CreateBuilder(args)
builder.Configuration.AddAzureKeyVault(
new Uri("https://wcf-keyvault.vault.azure.net/"),
new DefaultAzureCredential());
Note the Uri of the key vault name.
In theory, this does not break anything.
- If Key Vault is unreachable → app still loads
- If secret is found → it overrides file values
Step 6 – Remove ClientSecret from appsettings.json
Edit appsettings.json:
"AzureAd": {
"Instance": "https://WebCashFlow.ciamlogin.com/",
"Domain": "WebCashFlow.onmicrosoft.com",
"TenantId": "tenantID",
"ClientId": "clientID",
"CallbackPath": "/signin-oidc",
"SignedOutCallbackPath": "/signout-callback-oidc",
"SignedOutRedirectUri": "/",
"RemoteSignOutPath": "/signout-oidc"
}
- No code changes required elsewhere
- Configuration["AzureAd:ClientSecret"] still resolves
Step 7 – Test locally
- Sign in to Azure CLI: az login - What's this? See next section
- Run your Blazor Server app
- Attempt authentication
Expected result:
- Sign in works exactly as before
- No secrets on disk
- You can rotate the secret without redeploying
Azure CLI
These are the instructions for running the Azure CLI. Two commands have been suggested
Option 1 (Recommended): Azure Cloud Shell in the Azure Portal
This is the easiest and safest option — nothing to install. (But I'm not sure it would work for the 'Sign into Azure CLI: az login' in the Test locally scenario above.)
- Steps
- Go to https://portal.azure.com
- Log in
- In the top right toolbar, click the Cloud Shell icon ">_"
- When prompted:
- Choose Bash
- Create storage if asked (you can accept defaults)
- Run the command: az account show
Option 2: Local machine (actually, this is needed to Test Locally)
If you prefer running commands locally.
Step 1 – Install Azure CLI (if not already installed)
Step 2 – Open a terminal
- Windows
- PowerShell or Command Prompt
Step 3 – Log in
- az login
- This opens a browser window. Sign in with your Azure account.
Step 4 – Run the command
What output you should look for
The command returns JSON like this:
{
"id": "xxxxxxxx-xxxx-xxxx-xxxx-xxxxxxxxxxxx",
"name": "Pay-As-You-Go",
"tenantId": "yyyyyyyy-yyyy-yyyy-yyyy-yyyyyyyyyyyy",
"user": {
"name": "you@yourdomain.com",
"type": "user"
}
}
The important fields:
| Field |
Why it matters |
| tenantId |
This is the directory you are currently operating in |
| user.name |
Confirms who you’re logged in as |
| id |
Subscription being used |
Why run az login to test the application locally?
Short Answer:
You need to run az login locally because DefaultAzureCredential needs some identity to authenticate as, and on your local machine that identity usually comes from the Azure CLI login.
Long Answer:
What DefaultAzureCredential actually does:
DefaultAzureCredential does not magically authenticate by itself.
Instead, it tries a chain of possible credential sources in a fixed order and uses the first one that works.
Simplified, the order looks like this:
- Environment variables (e.g. AZURE_CLIENT_ID, AZURE_CLIENT_SECRET)
- Managed Identity (only works inside Azure: App Service, VM, Function, etc.)
- Visual Studio / Visual Studio Code login
- Azure CLI (az login)
- Azure PowerShell (Connect-AzAccount)
On a local development machine, steps 1 and 2 usually do not apply, so it eventually falls through to Azure CLI authentication.
This is why az login matters.
Why az login is required locally?
When you run:
builder.Configuration.AddAzureKeyVault(
new Uri("https://wcf-keyvault.vault.azure.net/"),
new DefaultAzureCredential());
Your app asks: “Who am I, and what identity should I present to Key Vault?”
On your local machine:
- There is no Managed Identity
- There may be no environment variables
- But there can be an Azure CLI login
When you run
az login
You are:
- Authenticating your Entra ID user account
- Storing a token securely in the Azure CLI cache
- Making yourself available as an identity provider
DefaultAzureCredential then:
- Detects the Azure CLI token
- Uses your signed in Entra ID user to request access tokens
- Calls Key Vault as you
What identity is being used after az login?
Your own Entra ID user account, not the app’s client secret. This is important.
- That means:
- Your user must have at least:
- Key Vault Secrets User, or
- Key Vault Secrets Officer, or
- an equivalent access policy / RBAC role
- This access is separate from your app’s production identity
This is by design and is considered best practice.
Why this is good practice:
- Security:
- You do not store client secrets locally
- No secrets in appsettings.json
- No secrets checked in to source control
- Environment separation
- • Local → uses developer identity
- • Azure → uses Managed Identity
- • No code changes required between environments
- Same code everywhere
Your code never changes; only where the identity comes from does.
What happens in Azure (production)?
When you deploy to Azure (App Service, Function App, etc.):
- DefaultAzureCredential stops at: ✅ Managed Identity
- az login is not used
- Your Entra ID application does not need the ClientSecret
- Key Vault access is granted to the Managed Identity
So this: new DefaultAzure
✅ Works locally
✅ Works in Azure
✅ No conditionals
✅ No secrets in config
Common misunderstanding about the ClientSecret
You mentioned: “I added a secret for my Azure Entra ID ‘ClientSecret'"
That secret is not being used locally if you are relying on az login.
It would only be used if:
- You explicitly configured ClientSecretCredential, or
- You set:
- AZURE_CLIENT_ID
- AZURE_TENANT_ID
Most modern ASP.NET guidance recommends not using client secrets at all if Managed Identity is available.
Summary
Why do I need az login locally?
- Because:
- DefaultAzureCredential needs an identity
- Locally, the simplest identity source is the Azure CLI
- az login provides that identity securely
- Your user account is used to access Key Vault
- This mirrors how Managed Identity works in Azure
My Conclusion
It's complicated - but it appears to work!
]]>